National sovereignty applies to cyberspace
- By Tang Lan
 0 Comment(s)
0 Comment(s) Print
Print E-mail China Daily, April 20, 2016
E-mail China Daily, April 20, 2016
|
|
|
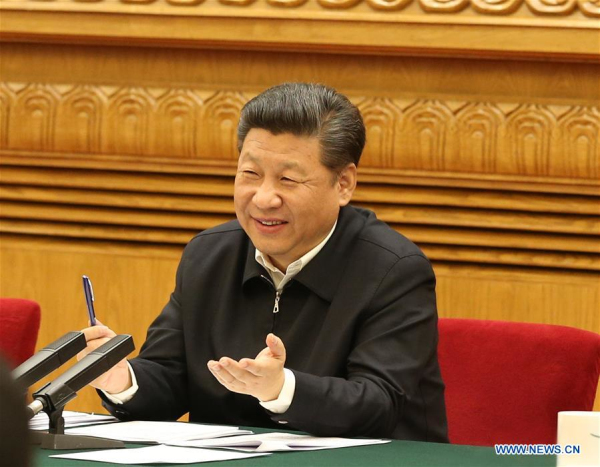
Chinese President Xi Jinping, also head of the central Internet security and informatization leading group, presides over a symposium on cyberspace security and informatization in Beijing, capital of China, April 19, 2016.[Photo/Xinhua] |
In A Declaration of the Independence of Cyberspace, a document that has been widely distributed since 1996, the author, John Perry Barlow, a founder of the Electronic Frontier Foundation, declared that the internet is free, open and equal, and called on governments to leave it alone.
Doubtlessly, the free nature of the internet prompted innovation in its early development. However, the virtual world is not independent of the real world, and the challenges of the virtual world originate in the real world.
It is a consensus of the international community that what applies offline, also applies online.
Therefore, the principle of national sovereignty and the international norms that derive from it should also apply to cyberspace.
National sovereignty is an essential concept of modern international law, and equality of sovereignty is a fundamental principle that defines contemporary international relations.
The question is how to apply the principle of national sovereignty in cyberspace.
The most direct way lies in jurisdiction. In 2003 and 2005, the UN held the two-stage World Summit on the Information Society, in which participant nations agreed that national sovereignty should determine decisions about internet-related public policies.
In 2013 and 2015, the UN information security Group of Governmental Experts discussed international rules for cyberspace, and there was hardly any dispute over applying the principle of national sovereignty.
The Tallinn Manual, written at the invitation of the Tallinn-based NATO Cooperative Cyber Defence Centre of Excellence to research how international law applies to cyber conflicts and cyber warfare, clearly states that: "A State may exercise control over cyber infrastructure and activities within its sovereign territory".






Go to Forum >>0 Comment(s)